The worlds of IT (Information Technology) and OT (Operational Technology) are converging and when implemented properly, can vastly improve efficiency, reduce errors, cut costs, and enhance workflows, greatly benefiting manufacturing, utility and energy companies, transportation, retail, medical, and communication industries. Apart from the advantages, this convergence also opens OT to a vast and advanced cyberthreat landscape.
These vulnerabilities pose a growing threat to critical infrastructure and other vital systems, as operations and safety can be seriously disrupted, it can lead to reputational damages as well. There is a myriad of challenges to fully secure an OT environment, and many approaches and architectures must be carefully considered before a decision can be made. Two of the most common security architectures used are zero trust and defense-in-depth approaches.
Zero Trust and Defense-in-Depth Security
Zero Trust security is a holistic approach requiring strict identity verification for every person and device trying to access resources on a network, whether inside or outside the network perimeter. The defense-in-depth approach contains a series of defensive mechanisms layers to protect valuable data and information. This multi-layered approach with intentional redundancies increases the security of a system as a whole, addressing many different attack vectors and a second chance to protect zones if the first layer of protection fails. By combining these two approaches, corporations can build with multiple layers of protection as the foundation and then add further protection using zero-trust mechanism to ensure access is restricted at every level.
Cybersecurity Awareness Enhancement
Another key approach is to realize the importance of enhancing cybersecurity awareness and mindset across all levels of an organization. All team members should be encouraged to understand the benefits of observing technical security requirements, in addition to coordinating security responses, network monitoring and management, and ensuring there are robust recovery and response processes, with the mindset assumption that all devices and networks can be compromised.
Strong Authentication Deployment
Deploying strong authentication is an additional critical approach for a network that utilizes zero trust architecture, which should include device access control, user authentication and authorization, and trust lists for IP addresses and service ports.
Network Segmentation Utilization
Appropriate network segmentation can prevent remote connection threats and insider threats from accessing the entire network. High-level network segmentation, such as deploying firewalls, can prevent malicious threats from moving laterally across the networks.
A firewall would assist administrators to establish zones in the network and allow only permitted traffic to transfer from one zone to another. Add on security policies and rules, such as IP addresses and only authorizing ports in use, to further segment the network into small, easier-to-manage sections to ensure that only necessary traffic is allowed.
A zero-trust model supports micro-segmentation, deployed through an Intrusion Prevention System (IPS), to enable the network to detect and prevent identified threats by containing cyberattacks within specific zones and protecting critical assets. The IPS would continuously monitor for possible malicious incidents to help reduce the spread of the attack and enable swift troubleshooting/restoration of the network.
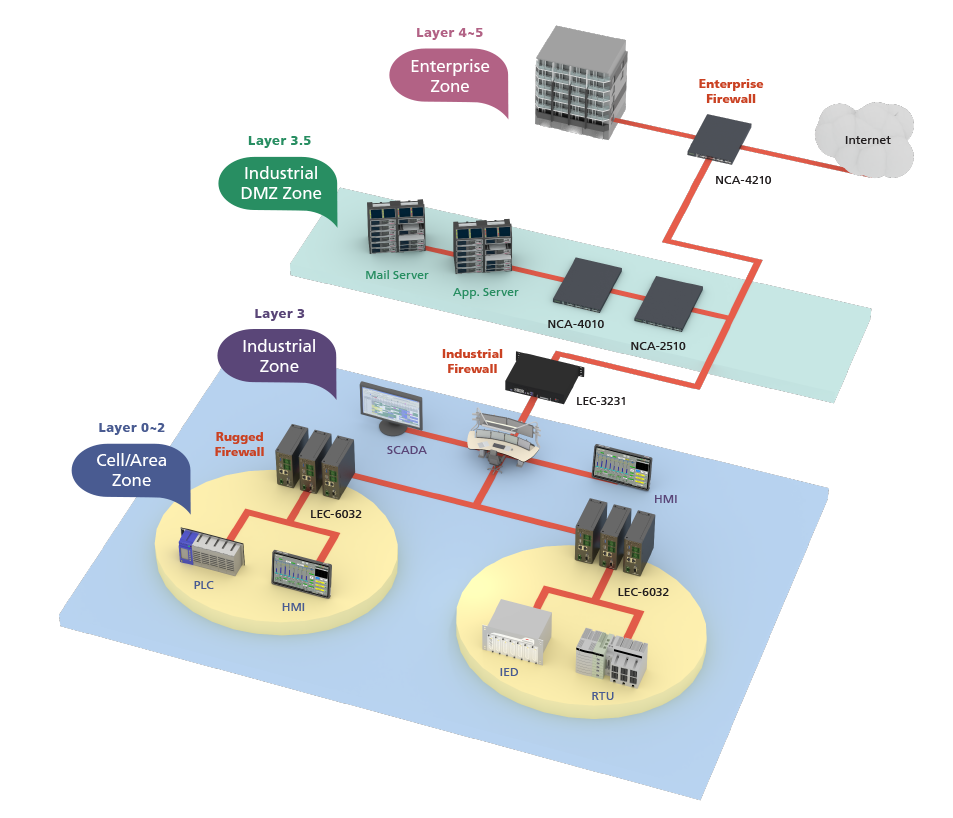
Lanner’s Network Security and Cybersecurity Solutions
There are multiple angles that must be considered to ensure a network is secure. Lanner has a wide range of box PCs to rugged industrial cyber security platforms to provide the needed network security protection for critical infrastructures. Lanner platforms have rich features to secure both IT and OT worlds with RPS high availability, advanced LAN bypass, multiple form factors, and wide operating temperatures. Lanner offers world-class industrial-grade network appliance powered by Intel® x86 to deliver the needed performance to execute security policies and instructions, to assist organizations realize their zero trust and defense-in-depth security networks. For detail, please visit Lanner website: https://www.lannerinc.com/products/network-appliances/industrial-security-appliances